“When entire divisions are shuttered simply because of disputes between political parties, the outcome is predictable: the United States grows more vulnerable, and critical infrastructure loses the protective buffer it once had.”
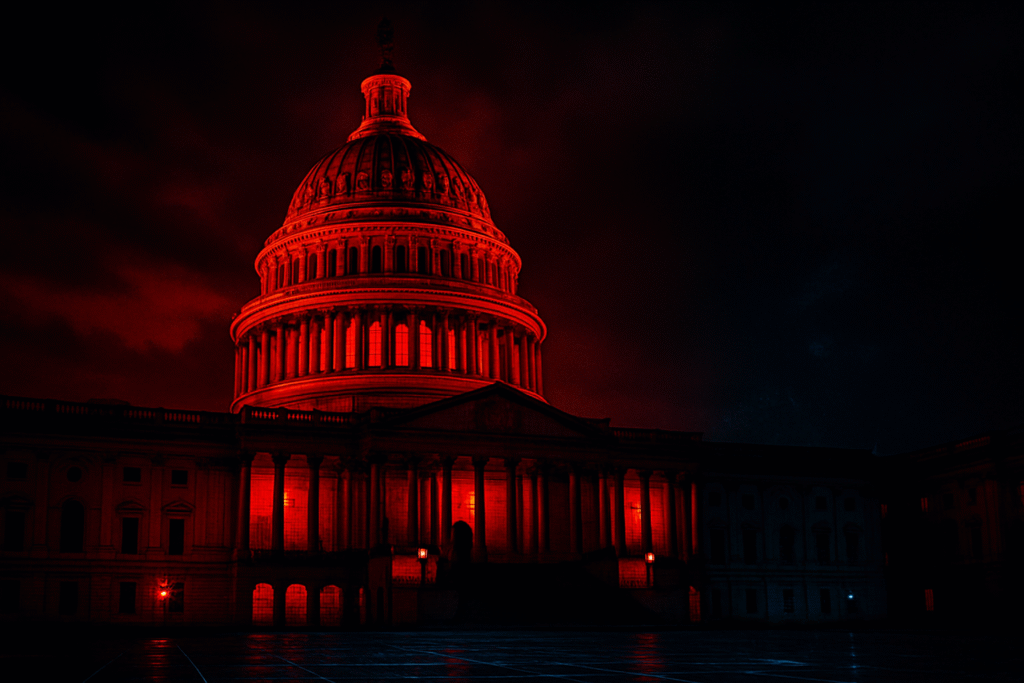
The Government Shutdown Is Weakening Cyber Defense
America’s digital defenses are facing their most dangerous test in 2025. With partisan gridlock halting funding and shutting down key agencies, the nation’s top cybersecurity professionals are being sidelined at the exact moment attackers are accelerating their campaigns. The result is not abstract, it is measurable, it is real, and it is already costing organizations millions.
Partisan Gridlock Leaves U.S. Networks Vulnerable to Attack
The ongoing shutdown of critical federal divisions, including large parts of the Cybersecurity and Infrastructure Security Agency (CISA), has left the nation with reduced monitoring and slower incident response. Staff furloughs mean fewer eyes on the networks at a time when attackers are ramping up. The fact that divisions responsible for protecting critical infrastructure are shuttered because of political disputes underscores the danger: cybersecurity has become collateral damage in Washington’s partisan battles.
The Human Factor: Losing Experts and Creating Insider Risks
Budget freezes and furloughs don’t just shrink capacity; they drive out the nation’s brightest cyber minds. Analysts and engineers who once defended U.S. infrastructure leave for private sector roles, or worse, become disillusioned insiders. A skilled operator who feels abandoned or betrayed can be as dangerous as any external attacker. The insider threat, amplified by political dysfunction, is a risk no one is talking about loudly enough.
Recent Cyber Attacks Show the Escalating Danger
While Washington stalls, adversaries are already taking advantage. In October 2025, nearly one billion Salesforce records were stolen in a sophisticated supply-chain style attack (Reuters). A dealership software firm breach exposed more than 766,000 clients (TechRadar). At the same time, global infostealer campaigns dumped 16 billion credentials tied to Google, Apple, and Facebook accounts, fueling massive account takeovers. Ransomware groups are also intensifying their focus on U.S. executives, launching targeted attacks during the shutdown window.
These incidents make one fact painfully clear: attackers strike when defenders are distracted. And right now, defenders are distracted by politics.
The Critical Role of Private-Sector Cybersecurity
With federal agencies sidelined, the burden has shifted to private companies to defend their own networks. Critical infrastructure; water utilities, hospitals, energy plants, manufacturers, and SaaS platforms, can no longer rely on federal alerts or rapid incident response. Flat networks, unpatched servers, and misconfigured cloud resources have become open invitations.
Redbot Security’s recent testing only underscores how immediate and actionable these risks are. In Q3 we discovered real-world, weaponizable flaws: Certificate Authority weaknesses (notably ESC1 and ESC8), legacy protocols that can enable domain compromise, and administrator credentials stored in cleartext on open shares. We also found basic operational gaps, no alerting for obvious indicators of compromise and missing server-side validation, that allowed SSRF and remote code execution paths to exist. Publicly exposed internal routing APIs provided direct paths to administrative account takeover, and widespread clear-text passwords and password reuse created straightforward routes to full domain compromise. These are not theoretical issues; they are the exact weaknesses ransomware gangs, nation-state actors, and malicious insiders are exploiting today.
Why Organizations Must Act Now
The average cost of a breach in 2024 reached $4.45 million (IBM). That number is rising in 2025, and with government defenses weakened, the private sector is absorbing the full brunt of this wave. Waiting for political clarity is not a strategy; it is surrender. Organizations must act now by validating their defenses through penetration testing, Red Teaming, and continuous monitoring.